Throughout a workshop on The Register, we’ve been looking at resiliency and security for hosted applications. The feedback we’ve had back is that a track record of security and privacy are at the heart of creating a feeling of trust towards a service provider.
What’s also plain is many feel that these issues are not at all well addressed by SaaS providers, coming right at the bottom of the pile of the strengths of the SaaS model over on-premise solutions. The result: there is a feeling of distrust and antipathy towards hosted applications.
So can’t we just continue without SaaS? The difficulty, of course, is that the way IT is deployed and used is changing dramatically. Once upon a time, it was easy to define the boundaries of IT services by the walls of the office – nowadays it’s not nearly so clear-cut.
More people have access to IT services as part of their normal routine, either from devices provided by the company, or personal devices. Employees are expecting to be able to log in from home, in any office or on the road, and at any time. Meanwhile new applications are changing how we do our jobs and interact with colleagues, partners and customers too.
With on-premise applications, the IT department is responsible for catering for these changes. Getting the applications up and running and having the basic functionality in place is the easier part – the headache is keeping it secure and available. And if we look closely at how we approach this, it is clear that all is not well.
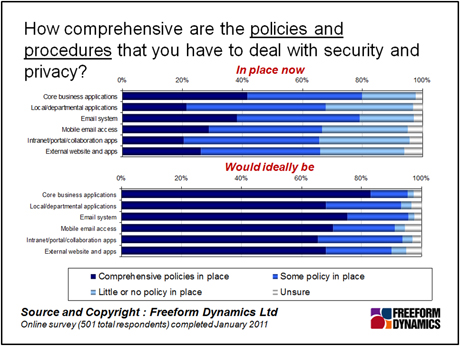
It is painful to realise that no matter how good our capabilities are for keeping things running and secure, most of us are far behind where we would ideally like to be – with security in particular being a problem.
While things are not necessarily bad, they are not all that good either. And this is a problem for IT, because improvements are time consuming and expensive unless security, privacy and safe remote access are architected right from the beginning. Even then, it is costly and demanding to get right.
It should come as no surprise that it is the core applications and communications platforms that have the smallest gap to the ideal. These are strategic platforms and typically receive the most investment and planning. This does, however, leave a whole tranche of applications that are neither very reliable nor highly secure.
If we look at where the biggest gaps are, with potentially the biggest risk of exposure, it is local and departmental applications, intranet and portal/collaboration platforms that are suffering. These are the applications that departmental users increasingly rely on to do their jobs effectively – yet they receive the least investment in security, as they are typically tactical applications that sit on the fringes of IT.
Is there any hope to improve things internally for these neglected applications? If history is anything to go by, the answer is likely to be “No”. Where central money is forthcoming, it will be better spent on improving the core applications and communications services, as they generally have a broader impact on the business and users.
Individual departments are unlikely to have the funding or the political clout to justify increasing the spend on improving their own situation. More importantly, especially with regards to security, our research shows that on the whole they do not care – they see it as someone else’s problem. The only way for these applications to improve is if IT as a whole invests to raise the capabilities of the entire application infrastructure, which is very costly to do.
So this brings us back to SaaS and the feeling of trust. You may feel that service providers are not able to provide the security and privacy that IT services need – but is this really true, or a case of double standards? You’ve told us that IT struggles to deliver, yet SaaS providers – at least those that hope to have a long term future – are geared up to do so precisely because it is their primary reason to be in business.
In the long term the problem is only going to get more acute. While SaaS is far from being perfect it is something that IT departments should be embracing, rather than resisting, as part of the arsenal for the next generation of collaboration.
CLICK HERE TO VIEW ORIGINAL PUBLISHED ON

Content Contributors: Andrew Buss