“The office” is fast becoming, for many organisations, a thing of the past – at least in terms of the expectation that it is the only place people go to work. If Ricky Gervais remade the series now, he’d have characters on trains trying to conduct negotiations over dodgy mobile signals, and web conferencing between people sitting in their underpants or loading the dishwasher.
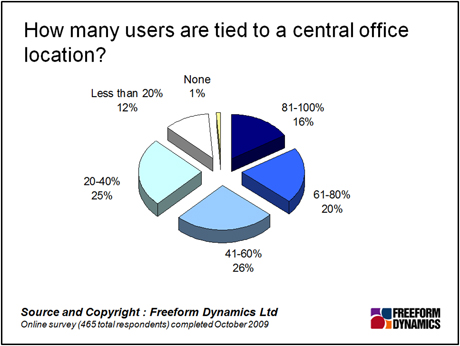
According to a poll we conducted a couple of months ago, only 16 per cent of respondent organisations have more than 80 per cent of their staff tied to a central office location:
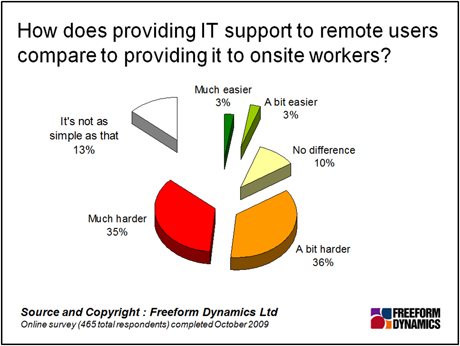
We’ve already established that identity management is no easy ride, but the problems are exacerbated by the remote working patterns the majority of us experience. Most of the day-to-day challenges manifest themselves in support calls, and we know from the same research that remote support is harder than onsite support:
There are other complications. If identity management is about ensuring that people only access authorised systems and data, your feedback tells us that remote workers are more likely to do silly things when away from the office – browse dodgy sites that come with malicious payloads, attempt access from a back street internet café in a strange town, and so on.
Indeed, considering the possible ways “your people” might access “your systems”, fragmentation is becoming the nature of the beast when it comes to remote working. This is not just about consumerisation – which incorporates the desire to use the latest gadget-bling – but also the needs-must attitude which leads to installing the VPN client on the home PC. Not that this is an identity management problem in itself, but if you’re not even sure what devices are used, or how secure they may be, how sure you can be that only the right people have access to the right resources?
The other side of the coin is that identity management is as much about ensuring access as preventing it. “Productivity” is a nebulous term, but we all know how it feels when a service is rendered inaccessible – email say, or the corporate address book, or a file share. Delays build up like cars on a motorway and before you know it a whole day has been lost. This can be both frustrating and costly, giving users a bad impression of IT services, which in turn creates problems at budget setting time. Users may also seek out unofficial work-arounds in the meantime, which may incorporate additional risks.
As before, part of the answer lies in understanding what information and systems access needs to be more rigidly controlled. Rather than sitting like King Canute on the beach and waiting for the tide of change to abate, it’s worth recognising that this is not a perfect world, and act accordingly. This is about balance: information and systems do need to be locked down, but on a scenario-by-scenario basis it’s worth looking at how business users can get their jobs done with the minimum of hurdles to jump.
Sometimes this will be about setting policy, some of which can be enforced – setting PIN numbers on smart phones for example. In others, specific technologies may help, such as two-factor authentication or the use of desktop virtualisation. Underlying any solution we need to build in that other identity management pre-requisite – auditability – so that a trail is maintained of who accessed what, when and how. Users’ lives, and the lives of anyone working a help desk, can be made much easier when you provide self-service facilities for password resets and management approvals for system access.
Given the pace of change, the bottom line can be summed up as “expect the unexpected”. However well you manage to lock down your existing environment, all it will take is an edict from a senior exec that his or her team needs to have the latest shiny gadget, or everyone should use Unified Communications, and all your efforts will be chaff in the wind. We may all be blown around by fashion; but we can nonetheless hold fast to the principles of identity management by focusing on the systems and information that matter, and ensuring they at least are provisioned, accessed and monitored in a traceable manner.
Content Contributors: Jon Collins
Through our research and insights, we help bridge the gap between technology buyers and sellers.





Have You Read This?
From Barcode Scanning to Smart Data Capture
Beyond the Barcode: Smart Data Capture
The Evolving Role of Converged Infrastructure in Modern IT
Evaluating the Potential of Hyper-Converged Storage
Kubernetes as an enterprise multi-cloud enabler
A CX perspective on the Contact Centre
Automation of SAP Master Data Management
Tackling the software skills crunch