We’re used to getting a hundred or so responses from the mini-polls we run, but the 383 responses to our recent encryption survey were indicative of just how important this area is to people. In it, we wanted to gauge the gap between aspiration and reality when it comes to encryption – what you think is necessary, versus what you have in place.
Up-front it’s worth reminding ourselves that online polls are self-selecting, that is, people don’t tend to respond unless they have an interest in the area. In this case, it’s fair to say that we’re going to get a good few people with an interest in IT security in general, not to mention encryption in particular, and the results should be read with this in mind.
Before we get onto the difference between expectation and reality, let’s consider what respondents told us were the drivers for encryption. As you can see in Figure 1, top of the list was compliance with regulations such as PCI. In addition, many of you are storing increasing amounts of sensitive data, and/or seeing an increasingly mobile workforce – and certain respondents are reacting to recent breaches.
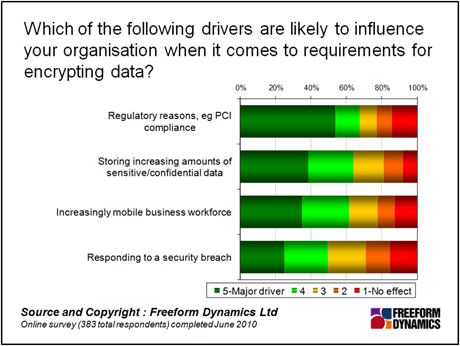
This is interesting enough – though perhaps it doesn’t tell us anything new. The tendrils of regulation are extending, the amount of data stored is growing and workers are increasingly mobile. For the record, answers to the “Other” option (not shown) tended to focus on customer pressure and perceptions, for example about reputation. We’ll come back to these drivers in a moment, but for now let’s look at the state of play across the sample as a whole. We can start to glean some value from this, not least in seeing where respondents felt attention should be spent (Figure 2).
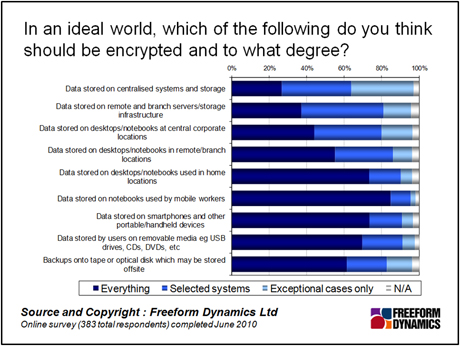
The top three ideal-world targets for encrypting everything are, in order:
•Data stored on notebooks used by mobile workers
•Data stored on smartphones and other portable/handheld devices
•Data stored on desktops/notebooks used in home locations
It’s no coincidence that all three are to do with distributed/mobile working. Keep in mind the self-selection factor – so the absolute levels of response in terms of current usage will be higher than those in a balanced sample. What’s more interesting is the relative gap between the ideal-world position and what’s actually in place (Figure 3).
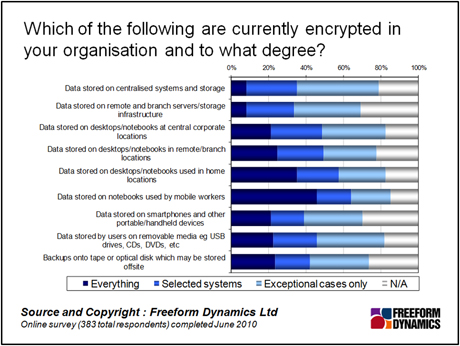
Looking at the delta between the ideal world and reality, clearly respondents believe that there is work still to be done across the board. The third point is how this figure relates to the first, “drivers” chart above. While compliance is seen as the top driver, the key areas where attention needs to be placed when it comes to encrypting data are all related to mobility. This is a fair indicator of how challenging the nature of the increasingly mobile workforce can be, when it comes to complying with regulations.
The executive who found himself personally responsible for a data breach when his laptop was stolen from his house may have been taken by surprise, as there is a lingering mindset that security is a central infrastructure thing. But rules and regs like PCI are not fussy about which particular part of the IT infrastructure is involved, be it a SAN in the data centre, or an SD card in a phone. It’s all just IT.
So, what drivers are most relevant when deciding where to place the emphasis when it comes to encryption? The answer is: “It’s not as simple as that.” When we compared these drivers against what organisations were actually up to with encryption, we didn’t find any one making a particular difference. The smart people I work with suggested coming up with an index based on the number of respondents that scored 4 or 5 for each of the options shown in Figure 1 above, from which we ended up with a subset of 77 respondents, for whom all four areas were seen as a major driver – let’s call this group the Focus group.
As you’d expect, the Focus group were more likely to feel the need for certain types of encryption, and indeed were more likely to have done something about it already. When we look at the ideal-world situation however, what this group gives us is a pretty stark view on how they believe things should be, particularly in the area of mobility (Figure 3).
Here’s the thing: the chart shows us that the Focus group believes that all data stored on notebooks used by mobile workers should be encrypted – or at least 95 per cent of the group believes this to be true. A smaller but still significant proportion believes this is also the case for computers used in home locations, data on handheld devices, and indeed data stored on USB sticks.
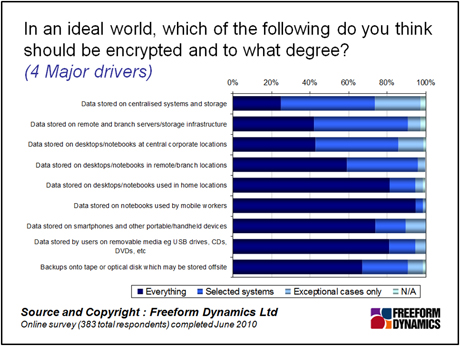
Fundamentally, the Focus group makes a pretty solid case for encryption in the mobile context, based on the drivers involved. Of course not all organisations will be quite so affected by the drivers – but we know these are things that are of growing concern to most. The implication is that as organisations face up to the challenges, they should be encrypting data across the range of mobile devices.
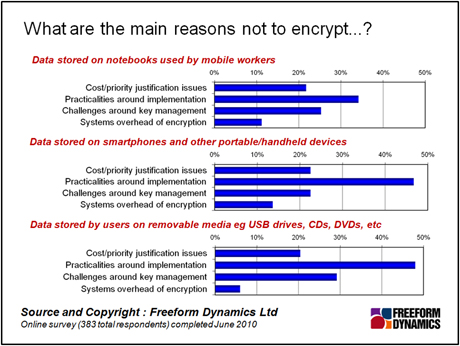
Or at least it would be, if it were simple to do. Interestingly, when we asked about the challenges involved, it turned out that cost was not the number one factor. This stands to reason given the increasing availability of low-cost encryption tools, including those built into operating systems. No, the number one reason according to respondents, involves practicalities around implementation – which are particularly challenging when it comes to mobile data (Figure 5). As we can see, this even trumps the key management issues that we are so often told pose a challenge.
So we have a dilemma. The Focus group recognise that mobile encryption should be switched on by default, and many organisations will reach the point where they too face the same drivers, to the same level. Right now, however, we are told that encryption remains too difficult to deploy, despite the availability of low-cost or bundled options.
The message to vendors is that they need to get their act together when it comes to simplifying encryption across the board – remember, we’re learning from a self-selecting sample of IT pros with an interest in security here, and not a bunch of random people from the street who might not have the technical smarts.
Meanwhile, the message to end-users is, if you haven’t already encrypted your laptop data, you’d best get on with it – or at least ask your IT department how to do it.
Content Contributors: Jon Collins
Through our research and insights, we help bridge the gap between technology buyers and sellers.





Have You Read This?
From Barcode Scanning to Smart Data Capture
Beyond the Barcode: Smart Data Capture
The Evolving Role of Converged Infrastructure in Modern IT
Evaluating the Potential of Hyper-Converged Storage
Kubernetes as an enterprise multi-cloud enabler
A CX perspective on the Contact Centre
Automation of SAP Master Data Management
Tackling the software skills crunch